A business email address functions as a digital credential, and it may be what sets yours apart from the competition.
How? One may ask.
Picture this: A procurement officer in Kampala receives two quotations for an office furniture supply contract worth UGX 45 million. The first arrives from . The second comes from .
Both quotations offer competitive pricing. Both promise quality delivery. Yet before reading a single line item, the procurement officer has already made assumptions about which company operates professionally and which one might be running operations from a bedroom.
Be it government tender submissions, corporate vendor applications, NGO partnership enquiries, or hotel booking confirmations, a sender’s email address can convey credibility or the absence of it before the message content is even read.
Due to the surge in internet usage in Uganda, Clients expect digital professionalism.
Banks request formal correspondence from business domains when processing loan applications. International partners verify organisational legitimacy, in part, through communication channels. Government procurement frameworks under PPDA guidelines also favour vendors who present formal business credentials, and yes, your email address counts as one of those credentials.
You might be running a legitimate operation with real inventory, genuine expertise, and excellent service delivery.
But if your first point of contact with a potential client is an email from a free consumer account, you are asking them to look past an immediate credibility gap.
Some will. Many will not, especially when your competitor’s quotation arrives from a proper business domain, and theirs looks like it belongs to an established entity.
What Exactly Is a Professional Business Email
A professional business email in Uganda or wherever uses your organisation’s domain name as its identifier. When a client sees , they immediately associate that communication with Kamu Construction Uganda as an entity.
The email address carries organisational identity.
Every email address consists of two parts separated by the @ symbol. The local part, which comes before the @, identifies the individual user or department. The domain part, after the @, identifies the organisation.
In a professional email, you control both parts. You decide that your sales enquiries go to and your managing director operates from .
With free consumer email services, you control only the local part, while Gmail, Yahoo, or Outlook retains the domain identity.
What a Complete Business Email in Uganda Setup Includes
Owning a domain name is the starting point, though a domain alone does not give you a functional email. A complete professional email setup requires several interconnected components working together.
First, you need a registered domain name. For Ugandan businesses, this typically means a .co.ug domain, a .ug domain, or an international domain like .com. The domain serves as your organisational identity online, whether or not you build a website on it.
Approximately 15,000 .ug domains were active as of 2023, reflecting growing adoption among Ugandan entities.
Second, you need a business email hosting platform. This is the service that actually receives, stores, and sends your email.
Microsoft 365, Google Workspace, Zoho Mail, and traditional web hosting providers like Hostcyclop.com all offer email hosting with varying features and price points. The platform provides the servers, storage, security infrastructure, and user interfaces that make email functional.
Third, proper DNS records must connect your domain to your email hosting platform. DNS (Domain Name System) records act as routing instructions.
When someone sends an email to , DNS records tell the internet which servers should receive that message.
Misconfigured DNS records mean emails never arrive, or worse, arrive inconsistently.
Fourth, authentication records (SPF, DKIM, and DMARC) verify that emails sent from your domain are legitimate.
These records protect your domain from being spoofed by malicious actors and ensure your legitimate emails reach recipients’ inboxes rather than spam folders. According to email security research, domains without proper authentication records experience deliverability rates up to 10% lower than properly configured domains.
Fifth, administrative control allows you to create, modify, and remove user accounts.
When you hire a new accountant, you create within minutes.
When an employee leaves, you restrict their access immediately and redirect their correspondence appropriately. This control is fundamental to organisational email management.
Prerequisites for Setting Up Business Email in Uganda
A Domain Name
Every professional email system begins with a registered internet domain. The domain serves as the organisational identifier that email servers use to route messages across global networks.
Domains follow formats such as companyname.co.ug or companyname.com, and they operate through the global Domain Name System (DNS) infrastructure, which manages over 360 million registered domains worldwide as of 2025.
In Uganda, businesses commonly register .co.ug domains through accredited registrars affiliated with the Uganda country code registry.
The domain becomes the foundation for email addresses such as , , and .
Think of the domain as the company’s permanent digital address. Every email account created later will be assigned to this identifier directly.
If your company operates a website, you might already own a domain. In many cases, businesses register the domain first for their website and later expand it into a full email system once staff communication requirements increase beyond two or three users.
Email Hosting Platform
Once the domain is registered, the next requirement is to select an email hosting platform that stores, processes, and delivers messages.
These platforms operate specialised mail servers responsible for authentication, spam filtering, storage management, and message routing across the internet. Global providers handle enormous traffic volumes.
Microsoft’s cloud email infrastructure processes over 8 trillion signals daily to detect spam and threats across enterprise mailboxes.
Common business email platforms in Uganda include Microsoft 365, Google Workspace, and Zoho Mail, as well as traditional hosting-based email services such as those offered by HostCyclop.
Each platform connects to the domain through DNS records and provides administrative dashboards where companies create user accounts, assign storage quotas, and manage security policies.
A small organisation with 10 employees typically requires between 10 and 20 active mailboxes, including departmental addresses and shared inboxes.
The hosting platform maintains these accounts and ensures reliable message delivery using standard Internet mail protocols.
DNS Configuration
The final foundational requirement involves DNS configuration, which links the domain to the selected email hosting platform.
DNS stands for Domain Name System, a distributed infrastructure that translates human-readable domain names into server locations used by internet services. The system handles billions of queries each day across global networks.
Email systems rely on Mail Exchange (MX) records, commonly called MX records, which instruct the internet how to deliver incoming messages for a domain.
When someone sends a message to , the sending server queries the domain’s MX records to determine the correct mail server to route it to. The process usually completes in less than 200 milliseconds, although changes can take several hours to propagate globally.
This configuration step often surprises business owners because it occurs behind the scenes.
You may never see these records during normal email use. Yet they quietly determine whether messages reach the correct mailbox or vanish into routing errors.
That small technical detail explains why many organisations prefer professional IT support when configuring their email infrastructure for the first time.
Best Business Email Solutions for Companies in Uganda
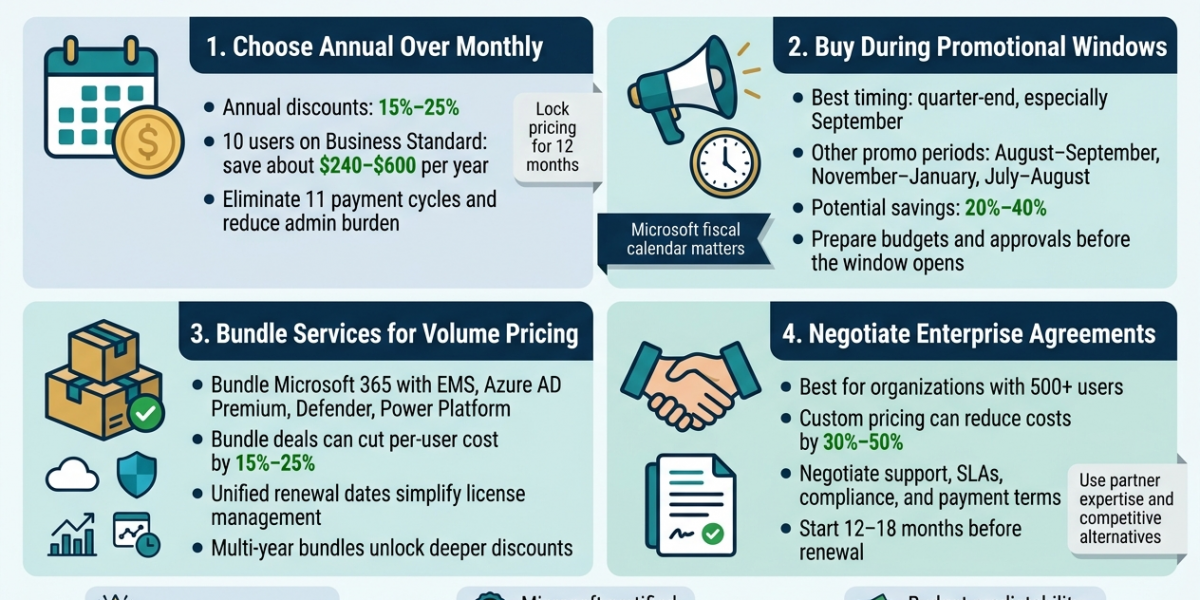
a) Microsoft 365 Business Email
Microsoft 365 operates its email service through a cloud platform called Exchange Online, which evolved from the Microsoft Exchange Server first introduced in 1996.
Today, the cloud version supports over 400 million active commercial users worldwide, according to Microsoft enterprise usage statistics.
Inside this environment, every employee receives a mailbox hosted within Microsoft’s global cloud infrastructure.
When an email is sent to , the sending mail server consults the domain’s MX records, which point toward Microsoft’s Exchange servers.
These servers authenticate the message, apply spam filtering, and then store it in the user’s mailbox database.
Each mailbox resides in Microsoft’s distributed storage system, where data is replicated across multiple data centres for reliability. An architecture of this sort allows organisations to maintain service availability above 99.9 percent, a standard requirement for enterprise communication systems.
From the administrator’s perspective, the company manages email accounts through the Microsoft 365 Admin Center.
Here, an IT manager can create user accounts, assign mailbox storage limits, configure security policies, and activate multi-factor authentication. A business with 40 employees, for example, can control all email permissions from a single dashboard.
You may recognise Outlook as the user interface employees use daily. Outlook connects to the Exchange server via MAPI over HTTPS, synchronising messages, calendars, and contacts across phones, laptops, and tablets in real time.
Behind the scenes, Microsoft also operates an advanced security layer called Microsoft Defender for Office 365, which analyses billions of signals daily to identify phishing attempts and malicious attachments before they reach employees’ inboxes.
b) Google Workspace
Google Workspace provides business email through Google’s Gmail infrastructure, one of the largest email systems in Uganda.
Gmail launched publicly in 2004, and the platform currently processes over 300 billion emails every day worldwide.
In a business environment, Gmail connects to the organisation’s domain rather than the public gmail.com address structure. This means that when someone sends a message to , the message routes through Google’s global mail servers while preserving the company’s domain identity.
Google’s infrastructure relies on a distributed computing architecture spread across dozens of global data centres.
Incoming messages pass through automated filtering engines that evaluate sender reputation, domain authentication records, and message structure. These systems block large volumes of spam before it reaches the recipient. Google estimates that its filtering technology stops over 99.9 percent of spam messages before they reach users’ inboxes.
For the user, the experience remains familiar. Employees access their mailboxes through the Gmail web interface or through mobile applications. However, the administrative side of the system operates through the Google Admin Console, where company administrators create user accounts, manage storage quotas, and configure security policies.
A company employing 15 staff members may create individual user accounts alongside shared departmental inboxes such as . These shared addresses often route messages to multiple staff members responsible for responding to customer enquiries.
Another important component of Google Workspace involves identity management. The same user account that controls Gmail access also manages access to Google Drive, Google Docs, and Google Meet meetings. This central identity system simplifies employee access management when staff join or leave the organisation.
c) Zoho Mail
Zoho Mail operates as part of the wider Zoho cloud application ecosystem developed by Zoho Corporation, a software company founded in 1996 that now supports over 90 million global users across its platforms.
Zoho Mail focuses heavily on structured email communication with simplified administration. The platform provides domain-based mailboxes, where each user receives storage allocations managed through the Zoho administration panel.
Email messages route through Zoho’s cloud mail servers once the domain’s MX records point toward Zoho infrastructure. Incoming messages pass through spam detection systems, authentication checks, and virus scanning engines before delivery into the recipient’s mailbox.
The system also supports industry-standard authentication protocols such as SPF, DKIM, and DMARC, which help receiving mail servers verify that messages originate from legitimate company domains. These authentication methods significantly reduce the likelihood of email spoofing attacks, a threat that affects thousands of business domains every year.
For example, a company operating 20 staff email accounts may configure SPF records to authorise only Zoho servers to send email on behalf of the company domain. This ensures external mail servers trust messages originating from that domain.
Zoho Mail environments frequently integrate with the broader Zoho business software ecosystem. Many companies connect their email system with Zoho CRM, allowing sales teams to track customer communication directly within their customer management database.
Hostcyclop Email Hosting
HostCyclop provides email services through traditional web hosting infrastructure, where the same server environment hosts both the company website and the domain email accounts. Hosted email systems have served small businesses since the early 2000s, particularly organisations with fewer than 25 employee accounts.
In this environment, email messages are stored on the same hosting server that manages the organisation’s website files. The hosting control panel allows administrators to create mailboxes such as or .
Incoming email arrives at the hosting server through standard Internet mail protocols such as SMTP for message delivery and IMAP or POP3 for mailbox retrieval. These protocols have been used across the internet email ecosystem since the late 1980s, and they remain widely supported by email applications today.
Employees can access these mailboxes through webmail interfaces or through email applications such as Outlook or mobile mail apps. When configured using IMAP, messages remain stored on the server while synchronising across multiple devices used by the employee.
This model works well for organisations operating a five- to ten-person team where email volume remains manageable and advanced collaboration tools are not a priority. Many small companies appreciate the straightforward nature of this setup. Website hosting, domain management, and email administration all operate from the same control panel, which simplifies day-to-day management.
Step by Step: How to Set Up a Professional Business Email in Uganda
Step 1: Register a Domain Name
The first step is to register a domain that will represent the organisation’s digital identity across websites and email systems.
Domains operate through the global Domain Name System, which currently manages more than 360 million registered domains worldwide, according to industry registry reports.
Businesses in Uganda often register domains using extensions such as .co.ug, .com, or .org, depending on organisational preference.
Once registered, the domain serves as the basis for all future email addresses within the company. Examples include , , and .
A domain registration usually takes less than 10 minutes to complete through an accredited registrar, although official ownership records may take several hours to propagate across global DNS servers.
Step 2: Choose an Email Hosting Platform
After securing the domain, the organisation selects an email hosting platform to store messages, manage user accounts, and process email traffic.
These systems operate specialised mail servers designed to handle authentication, encryption, spam filtering, and message delivery.
Common platforms include Microsoft 365, Google Workspace, and Zoho Mail, as well as hosting-based services from providers such as HostCyclop.
Each platform connects to the domain through DNS records that direct incoming messages to the correct mail server.
A company with 20 employees, for instance, typically provisions at least 20 individual mailboxes alongside departmental addresses such as support@ or accounts@.
The hosting provider provides administrative tools that allow managers or IT staff to create and manage these accounts through a central dashboard.
Selecting the platform often depends on collaboration needs, storage requirements, and administrative preferences.
Some organisations prefer integrated productivity tools within the email platform, while others focus primarily on reliable message delivery and account management.
Step 3: Verify Domain Ownership
Email providers require confirmation that the organisation legitimately owns the domain before activating domain-based email services.
Verification protects against fraudulent attempts to create mail systems using domains belonging to other organisations.
The process typically involves adding a TXT record to the domain’s DNS settings. This record contains a verification string generated by the email provider.
Once the record appears in the DNS system, the provider automatically confirms domain ownership.
DNS updates propagate gradually across the Internet infrastructure. In most cases, verification completes within 15 minutes to 2 hours, although global propagation can extend up to 24 hours, depending on DNS caching policies used by various internet service providers.
Step 4: Configure Mail Exchange Records
Once verification is complete, administrators configure the domain’s Mail Exchange (MX) records. These records instruct the global email system where messages for the domain should be delivered.
For example, if someone sends a message to , the sending server queries the domain’s MX records to determine the correct mail server destination.
The lookup process usually completes in under 200 milliseconds, which explains why email delivery appears almost instantaneous to users.
Each email provider supplies specific MX record values that must be entered in the domain’s DNS management panel. Once these records propagate across global DNS servers, incoming messages begin routing directly to the organisation’s chosen email platform.
Step 5: Create Email Accounts
After the domain routing configuration is complete, administrators begin creating user accounts for employees. Each account receives its own mailbox, login credentials, and storage allocation within the hosting platform.
A growing organisation with 30 staff members often creates both individual accounts and functional departmental addresses. Examples include , , and . Shared mailboxes allow multiple employees to manage incoming messages from a single communication channel.
At this stage, the email system begins to resemble the company’s internal communication structure. Sales inquiries reach the sales team, financial communications flow into accounting departments, and management correspondence arrives in executive inboxes.
Step 6: Connect Email to Devices
The final operational step is to connect employee devices to their newly created mailboxes. Staff typically access business email in Uganda through applications such as Outlook, web browsers, or mobile email apps installed on smartphones.
Modern email platforms support synchronisation protocols that keep messages, calendars, and contacts up to date across multiple devices. An employee reading a message on their phone will see the same message already marked as read on their laptop seconds later.
Many organisations deploy email access across three primary device categories: office computers, employee smartphones, and web browser access via secure login portals. Once these connections are configured, the company’s professional email system begins functioning as a central communication hub for daily operations.
Business Email Best Practices Companies in Uganda
Use Role-Based Email Addresses
Many organisations begin with individual employee accounts, yet operational efficiency improves when companies introduce role-based addresses tied to business functions. Examples include , , and .
These addresses function as shared communication channels rather than personal inboxes.
Consider a small Ugandan trading company with 12 employees handling procurement, sales inquiries, and supplier invoices every day.
Routing these messages into dedicated departmental inboxes ensures continuity even when individual staff members change roles or leave the organisation.
You will notice another advantage during customer interaction. Clients remember functional addresses more easily than personal names.
When someone needs assistance months later, sending a message to feels intuitive and reliable.
Implement Strong Email Security Controls
Email systems remain one of the most common entry points for cyber incidents affecting businesses worldwide.
Industry research from Verizon’s 2024 Data Breach Investigations Report indicates that roughly 36 percent of security breaches involve phishing or email-based attacks.
Organisations therefore apply layered protection mechanisms to business email platforms in Uganda. These measures often include multi-factor authentication, spam filtering, and domain authentication protocols such as SPF and DKIM.
Together, these systems verify sender legitimacy and prevent malicious messages from entering employee inboxes.
Security configuration sometimes feels like background maintenance that nobody notices until something goes wrong. Yet a single compromised mailbox can expose sensitive invoices, supplier contracts, and customer communication records.
That risk explains why IT administrators treat email security policies as core infrastructure rather than optional settings.
Standardise Email Signatures
Professional email systems allow organisations to deploy standardised signatures across employee accounts. These signatures provide consistent contact information and reinforce company identity in every outgoing message.
A typical signature contains the sender’s name, role, phone number, company name, and website address.
Many organisations also include compliance notices or confidentiality statements, especially when handling legal or financial communication.
In companies with 20 or more staff members, centralised signature policies help maintain consistency across hundreds of daily emails.
You might think of the signature as a digital business card automatically attached to every message. Recipients immediately see who they are speaking with and how to continue the conversation through phone or other channels.
Common Business Email Mistakes Companies Make in Uganda
1. Weak Password and Authentication Practices
One of the most common operational risks in company email systems involves weak authentication practices.
Many employees still create simple passwords containing predictable patterns, despite modern security recommendations.
Cybersecurity studies conducted by Microsoft indicate that enabling multi-factor authentication blocks more than 99 percent of automated credential attacks targeting business accounts. Yet many organisations delay implementing this protection because employees perceive the login process as inconvenient.
If your company relies on email for invoices, supplier negotiations, and internal approvals, the mailbox essentially becomes a gateway to financial information.
That reality explains why strong authentication practices remain central to responsible IT management.
2. Missing Domain Authentication Records
Email systems rely on several authentication mechanisms that verify the legitimacy of messages sent from a domain.
Two of the most widely used standards include SPF and DKIM, which confirm that the sending server has permission to send messages on behalf of the domain.
Without these records configured, receiving mail servers may flag legitimate company messages as suspicious or route them into spam folders.
Global email filtering systems process over 300 billion messages each day, and automated verification plays a central role in sorting legitimate communication from malicious traffic.
Businesses sometimes discover this issue when customers mention missing quotations or unanswered support emails. In many cases, the messages existed but were caught by spam filters because authentication records were incomplete.
3. Lack of Mailbox Management Policies
As companies grow, email systems accumulate large volumes of stored messages and attachments. Without mailbox management policies, storage usage increases quickly, making administrative oversight difficult.
An employee receiving 50 emails per day will accumulate more than 18,000 messages annually, not including attachments and forwarded communication threads.
Multiply this across several departments, and the organisation’s email archive grows to hundreds of thousands of items.
Many companies address this operational challenge by implementing retention policies, managing shared mailboxes, and practising periodic inbox organisation.
These measures ensure that email remains a functional communication tool rather than an unmanageable archive of historical messages.
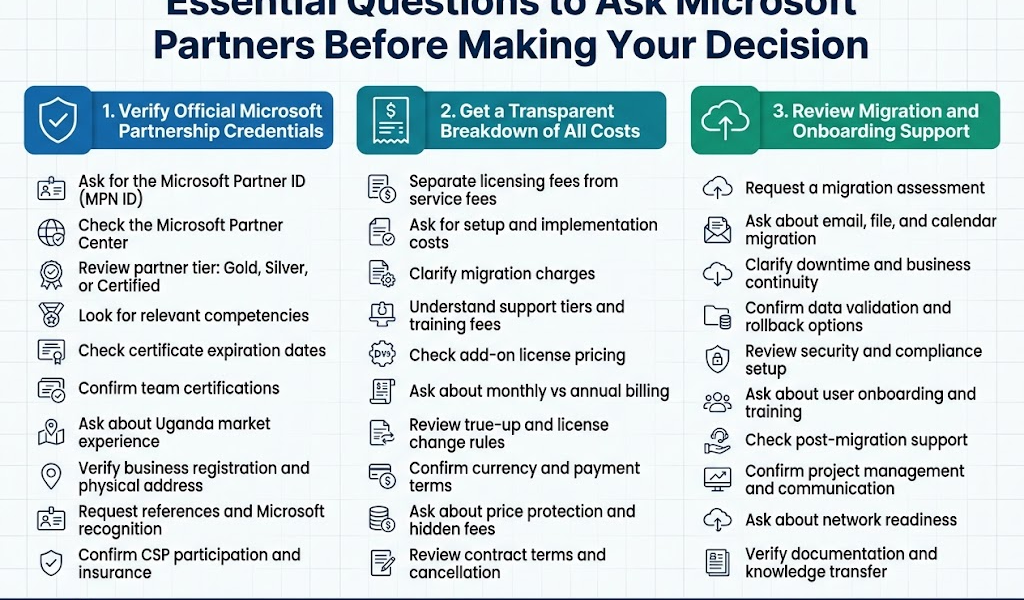
Why work with Othware
Professional business email functions as a foundational communication system within modern organisations in Uganda. Messages flow through domain-controlled mail servers, authentication systems verify sender identity, and structured inboxes support daily coordination between employees, clients, and suppliers.
Given that global email traffic exceeds 347 billion messages daily, reliable configuration and management quickly become operational necessities for any company participating in digital commerce.
For many Ugandan businesses, establishing that infrastructure marks an important step in organisational maturity.
Domain-based email systems bring order to internal communication, enhance credibility in client interactions, and provide secure channels for exchanging documents and financial information.
Implementing these systems, however, often involves several interconnected technical steps. Domain registration, DNS configuration, mailbox provisioning, and security policies all operate within the same ecosystem. A small oversight in one configuration layer can affect message delivery, resulting in hundreds of emails per week.
That is why many organisations prefer guidance from experienced IT professionals during setup and ongoing management.
With years of experience supporting businesses across Kampala, Entebbe, and beyond, Othware Uganda helps organisations deploy professional email systems that are secure, reliable, and tailored to local operational realities.
Our team manages the entire setup process, from domain verification and DNS configuration to mailbox creation and multi-layer security policies, ensuring your system functions efficiently from day one.
We work with platforms such as Microsoft 365, Google Workspace, and Zoho Mail, guiding you in selecting the solution that best fits your business size, workflow, and collaboration needs.
Beyond setup, we provide ongoing technical support to help your team connect devices, manage accounts, and maintain security standards without disrupting daily operations.
We believe your email system should empower your business rather than complicate it. By handling the technical complexity, we allow you to focus on running your organisation while ensuring that every message sent reflects professionalism, credibility, and operational integrity.
Get started today with Othware Uganda and secure your professional email infrastructure. Contact us to configure your domain, set up mailboxes, and ensure seamless, secure communication for your business.

Passionate about tech, a better writer than talker. Also a Content writer @ Othware.